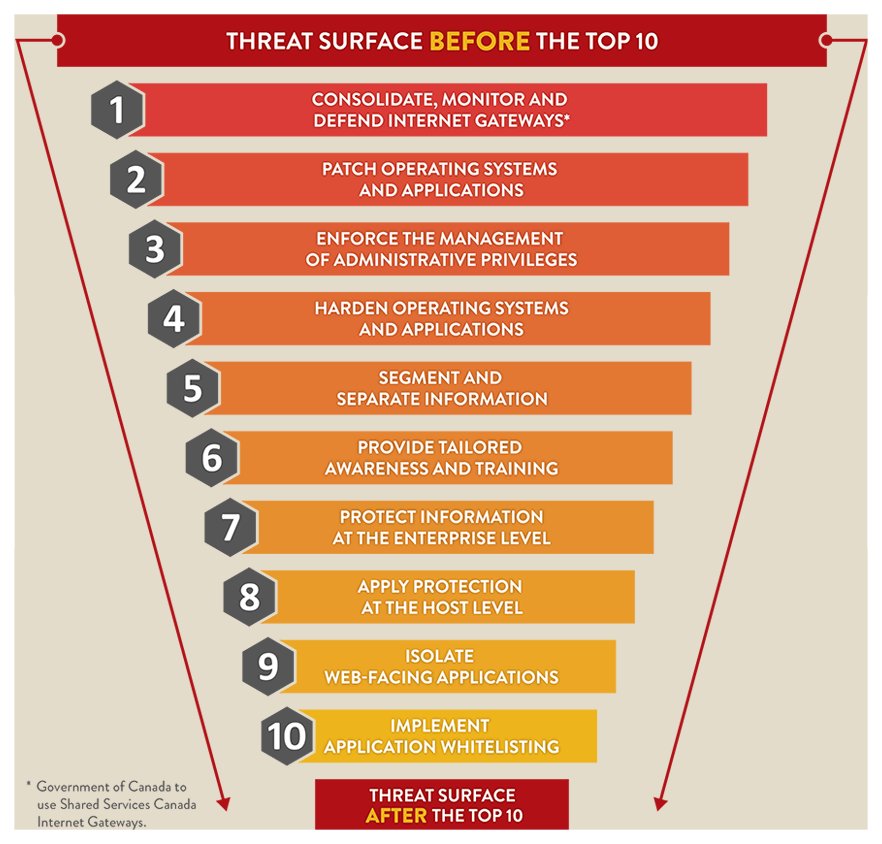
Canadian Centre for Cyber Security on Twitter: "The Top 10 Information Technology Security Actions are effective. Organizations that implement these recommendations will address many vulnerabilities and counter most current cyber threats ...

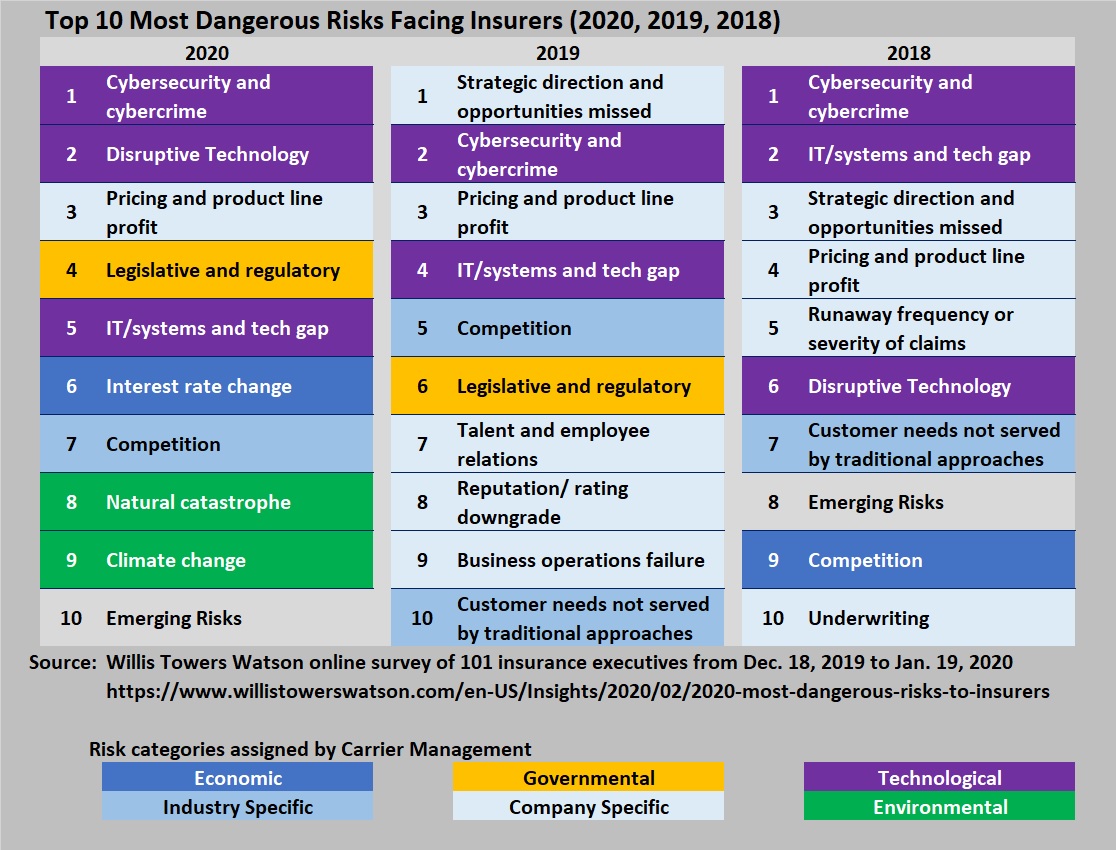
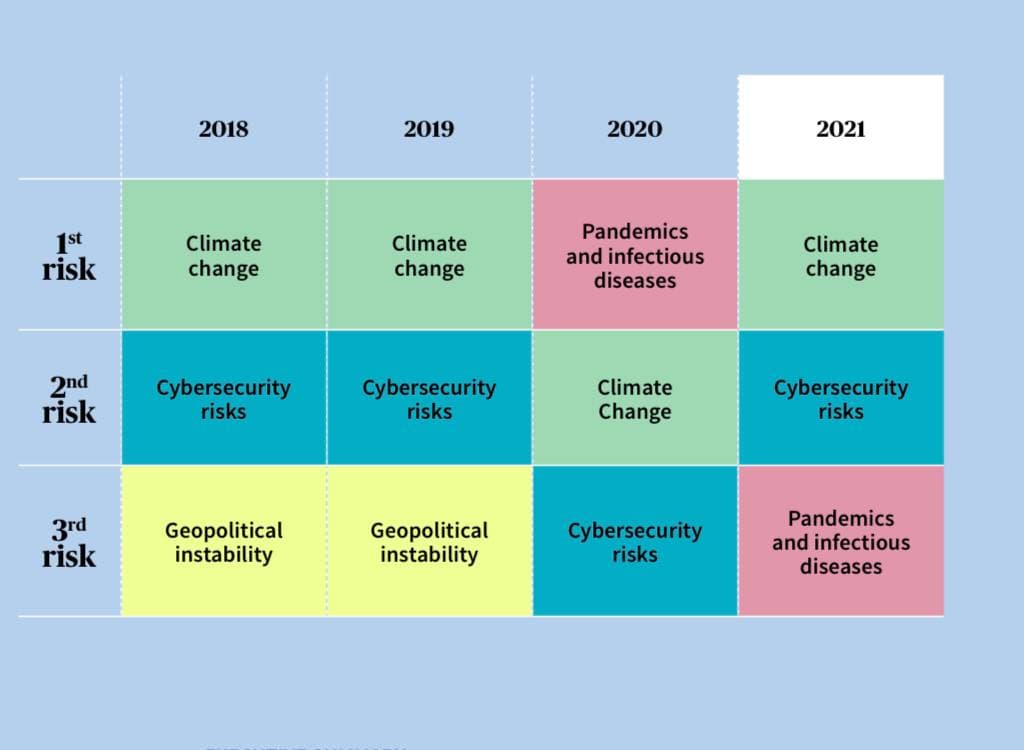
Technology, Natural Disasters, Cyber Breaches Dominate Risks Facing the Boardroom | 2018-02-05 | Security Magazine
.png)